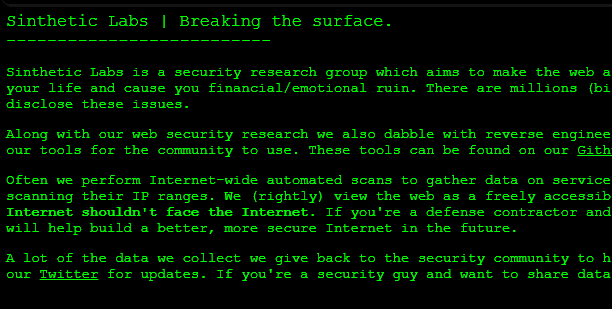
About Sinthetic Labs
Sinthetic Labs is a security research group which aims to make the web a safer place by taking an offensive approach to security. Focusing mainly on web security, we take on the role of a malicious hacker who wants to destroy your life and cause you financial/emotional ruin. There are millions (billions?) of vulnerabilities and security issues which exist due to years of poor programming, ignorance, and laziness. Watch as we discover, exploit, and disclose these issues.
Along with our web security research we also dabble with reverse engineering, OSINT, penetration testing, software auditing, and software development (primarily security related tools). Every so often we open-source some of our tools for the community to use. These tools can be found on our Github page and you can report bugs there too. For updates, new releases, and lots of other information you can follow us on Twitter.
Often we perform Internet-wide automated scans to gather data on services facing the Internet and vulnerable software. We do try to minimize the impact of these scans, and we do appreciate some organizations don’t want us scanning their IP ranges. We (rightly) view the web as a freely accessible resource for everyone to use. Each IP we scan is public with the implication that it can be accessed by anyone. Services which don’t need to face the Internet shouldn’t face the Internet. If you’re a defense contractor and I can access the control panel for your military drones, you’re doing something wrong. You’re always free to drop our requests but the research we do will help build a better, more secure Internet in the future.
A lot of the data we collect we give back to the security community to help understand, mitigate, and risk assess attacks and vulnerabilities. You can find more information and even download this data on our Twitter for updates. If you’re a security guy and want to share data or collaborate on projects, send us a message. We’d love to see what you’re working on.
A look inside Facebook’s source code
Note: None of the code in this post was obtained illegally, nor given to me directly by any Facebook employee at any time.
I’ve always been a fan of Facebook from a technical point of view. They contribute a lot to the open source community and often open source their internal software too. Phabricator, libphutil, and XHP are great examples of that. For a while I contributed a bit to both Phabricator and XHP, and I ended up finding out a lot more about Facebook’s internals than I intended. Read on…
It was mid-2013 and I was busy fixing a few bugs I had encountered while using Phabricator. If my memory serves me correctly the application was throwing a PhutilBootloaderException. I didn’t have much knowledge of how Phabricator worked at the time so I googled the error message. As you’d expect I came across source code and references, but one specific link stood out. It was a Pastebin link.
Of course, this intrigued me. This is what I found…
[emir@dev3003 ~/devtools/libphutil] arc diff --trace
>>> [0] <conduit> conduit.connect()
<<< [0] <conduit> 98,172 us
>>> [1] <exec> $ (cd '/home/emir/devtools/libphutil'; git rev-parse --show-cdup)
<<< [1] <exec> 13,629 us
>>> [2] <exec> $ (cd '/home/emir/devtools/libphutil/'; git rev-parse --verify HEAD^)
<<< [2] <exec> 17,024 us
>>> [3] <exec> $ (cd '/home/emir/devtools/libphutil/'; git diff --no-ext-diff --no-textconv --raw 'HEAD^' --)
>>> [4] <exec> $ (cd '/home/emir/devtools/libphutil/'; git diff --no-ext-diff --no-textconv --raw HEAD --)
>>> [5] <exec> $ (cd '/home/emir/devtools/libphutil/'; git ls-files --others --exclude-standard)
>>> [6] <exec> $ (cd '/home/emir/devtools/libphutil/'; git ls-files -m)
<<< [5] <exec> 73,004 us
<<< [6] <exec> 74,084 us
<<< [4] <exec> 77,907 us
<<< [3] <exec> 80,606 us
>>> [7] <exec> $ (cd '/home/emir/devtools/libphutil/'; git log --first-parent --format=medium 'HEAD^'..HEAD)
<<< [7] <exec> 16,390 us
>>> [8] <conduit> differential.parsecommitmessage()
<<< [8] <conduit> 106,631 us
Linting...
>>> [9] <exec> $ (cd '/home/emir/devtools/libphutil'; git rev-parse --show-cdup)
<<< [9] <exec> 9,976 us
>>> [10] <exec> $ (cd '/home/emir/devtools/libphutil/'; git merge-base 'HEAD^' HEAD)
<<< [10] <exec> 13,472 us
>>> [11] <exec> $ (cd '/home/emir/devtools/libphutil/'; git diff --no-ext-diff --no-textconv --raw '00645a0aec09edc7f0f1f573032991ae94faa01b' --)
>>> [12] <exec> $ (cd '/home/emir/devtools/libphutil/'; git diff --no-ext-diff --no-textconv --raw HEAD --)
>>> [13] <exec> $ (cd '/home/emir/devtools/libphutil/'; git ls-files --others --exclude-standard)
>>> [14] <exec> $ (cd '/home/emir/devtools/libphutil/'; git ls-files -m)
<<< [11] <exec> 19,092 us
<<< [14] <exec> 15,219 us
<<< [12] <exec> 21,602 us
<<< [13] <exec> 43,139 us
>>> [15] <exec> $ (cd '/home/emir/devtools/libphutil/'; git diff --no-ext-diff --no-textconv -M -C --no-color --src-prefix=a/ --dst-prefix=b/ -U32767 '00645a0aec09edc7f0f1f573032991ae94faa01b' --)
<<< [15] <exec> 28,318 us
>>> [16] <exec> $ '/home/engshare/devtools/libphutil/src/parser/xhpast/bin/xhpast' --version
<<< [16] <exec> 11,420 us
>>> [17] <exec> $ '/home/engshare/devtools/arcanist/scripts/phutil_analyzer.php' '/home/emir/devtools/libphutil/src/markup/engine/remarkup/markuprule/hyperlink'
<<< [17] <exec> 490,196 us
>>> [18] <exec> $ '/home/engshare/devtools/arcanist/scripts/phutil_analyzer.php' '/home/engshare/devtools/libphutil/src/markup'
>>> [19] <exec> $ '/home/engshare/devtools/arcanist/scripts/phutil_analyzer.php' '/home/engshare/devtools/libphutil/src/markup/engine/remarkup/markuprule/base'
>>> [20] <exec> $ '/home/engshare/devtools/arcanist/scripts/phutil_analyzer.php' '/home/engshare/devtools/libphutil/src/parser/uri'
>>> [21] <exec> $ '/home/engshare/devtools/arcanist/scripts/phutil_analyzer.php' '/home/engshare/devtools/libphutil/src/utils'
<<< [18] <exec> 498,899 us
<<< [19] <exec> 497,710 us
<<< [20] <exec> 517,740 us
<<< [21] <exec> 556,267 us
>>> [22] <exec> $ '/home/engshare/devtools/libphutil/src/parser/xhpast/bin/xhpast'
<<< [22] <exec> 10,066 us
LINT OKAY No lint problems.
Running unit tests...
HipHop Fatal error: Uncaught exception exception 'PhutilBootloaderException' with message 'The phutil library '' has not been loaded!' in /home/engshare/devtools/libphutil/src/__phutil_library_init__.php:124\nStack trace:\n#0 /home/engshare/devtools/libphutil/src/__phutil_library_init__.php(177): PhutilBootloader->getLibraryRoot()\n#1 /home/engshare/devtools/arcanist/src/unit/engine/phutil/PhutilUnitTestEngine.php(53): PhutilBootloader->moduleExists()\n#2 /home/engshare/devtools/arcanist/src/workflow/unit/ArcanistUnitWorkflow.php(113): PhutilUnitTestEngine->run()\n#3 /home/engshare/devtools/arcanist/src/workflow/diff/ArcanistDiffWorkflow.php(1172): ArcanistUnitWorkflow->run()\n#4 /home/engshare/devtools/arcanist/src/workflow/diff/ArcanistDiffWorkflow.php(225): ArcanistDiffWorkflow->runUnit()\n#5 /home/engshare/devtools/arcanist/scripts/arcanist.php(257): ArcanistDiffWorkflow->run()\n#6 {main}Okay — so this isn’t exactly source code. It’s just some command line output. But it does tell us some interesting information.
- The person who, likely, posted this was “emir”. This may be the person’s first name, or it could be their first initial and then their surname (E. Mir). It’s clear this output was intended to be seen by another engineer at Facebook, so posting it on Pastebin probably wasn’t the smartest move. This person may have made other slip ups which could make them a target if an attacker sees an opportunity.
- “dev3003” is the name of the machine emir was working on at the time. This tells us Facebook has at least 3,000 machines reserved for development (assuming “3003” increments from 1, which I’m quite sure it does).
- `/home/engshare/devtools/` is the path where libphutil and arcanist are installed. `/home/engshare/` is shared between the development machines via NFS if I remember correctly. Nothing overly interesting here, but there are likely other internal scripts located in that directory.
- There’s also some information about execution times and Git hashes which could be of use but nothing I’d personally look in to.
After this find, I went ahead and tried to similiar pastes which had to been made. I was not disappointed.
[25/10/2013] Promoting The Meme Bank (1/1) - Campaign Update Failed: Campaign 6009258279237: Value cannot be null (Value given: null) TAAL[BLAME_files,www/flib/core/utils/enforce.php,www/flib/core/utils/EnforceBase.php]Now, this looks to be an exception which was caught and logged. What’s interesting here is it shows us file names and paths. “flib” (Facebook Library) is an internal library which contains useful utilities and functions to help with the development. Let’s go deeper..
[ksalas@dev578 ~/www] ./scripts/intl/intl_string.php scan .
Loading modules, hang on...
Analyzing directory `.'
Error: Command `ulimit -s 65536 && /mnt/vol/engshare/tools/fbt_extractor -tasks 32 '/data/users/ksalas/www-hg'' failed with error #2:
stdout:
stderr:
warning: parsing problem in /data/users/ksalas/www-hg/flib/intern/third-party/phpunit/phpunit/Tests/TextUI/dataprovider-log-xml-isolation.phpt
warning: parsing problem in /data/users/ksalas/www-hg/flib/intern/third-party/phpunit/phpunit/Tests/TextUI/dataprovider-log-xml.phpt
warning: parsing problem in /data/users/ksalas/www-hg/flib/intern/third-party/phpunit/phpunit/Tests/TextUI/log-xml.phpt
warning: parsing problem in /data/users/ksalas/www-hg/scripts/sandcastle/local_testing/script_for_test_commits.php
warning: parsing problem in /data/users/ksalas/www-hg/lib/arcanist/lint/linter/__tests__/hphpast/php-tags-script.lint-test
LEXER: unrecognised symbol, in token rule:'
warning: parsing problem in /data/users/ksalas/www-hg/scripts/intern/test/test.php
warning: parsing problem in /data/users/ksalas/www-hg/scripts/intern/test/test2.php
Fatal error: exception Common.Todo
Fatal error: exception Sys_error("Broken pipe")
Type intl_string.php --help to get more information about how to use this script.Now we’re getting to the good stuff. We have ksalas on dev578 running what seems to be a string parser. `intl_string.php` tries to run `/mnt/vol/engshare/tools/fbt_extractor`, so we know for sure there are some other scripts in `/mnt/vol/engshare/`. We can also see they use PHP Unit for unit testing, and “www-hg” shouts Mercurial to me. It’s well known they moved from Subversion to Git — I’d put money on it that they’ve been expiermenting with Mercurial too at some point.
“That’s still not god damn source code!” I hear you cry. Don’t worry, someone posted some on Pastebin too.
Index: flib/core/db/queryf.php
===================================================================
--- flib/core/db/queryf.php
+++ flib/core/db/queryf.php
@@ -1104,11 +1104,12 @@
* @author rmcelroy
*/
function mysql_query_all($sql, $ok_sql, $conn, $params) {
+ FBTraceDB::rqsend($ok_sql);
switch (SQLQueryType::parse($sql)) {
case SQLQueryType::READ:
$t_start = microtime(true);
$result = mysql_query_read($ok_sql, $conn);
$t_end = microtime(true);
$t_delta = $t_end - $t_start;
if ($t_delta > ProfilingThresholds::$queryReadDuration) {
ProfilingThresholds::recordDurationError('mysql.queryReadDuration',The file in question is `flib/core/db/queryf.php`. At first glance we can tell it’s a diff of a file which contains a bunch of MySQL-related functions. The function we can see here, `mysql_query_all()`, was written by rmcelroy. From what I can see in the code it’s pretty much a simple function which executes a query, with a little custom logging code. It may be more complex but unfortunately we may never know. 🙁
I’ll post a few more example of code I’ve found, all of which (and more) can be downloaded from the bottom of this post.
diff --git a/flib/entity/user/personal/EntPersonalUser.php b/flib/entity/user/personal/EntPersonalUser.php
index 4de7ad8..439c162 100644
--- a/flib/entity/user/personal/EntPersonalUser.php
+++ b/flib/entity/user/personal/EntPersonalUser.php
@@ -306,13 +306,15 @@ class EntPersonalUser extends EntProfile
public function prepareFriendIDs() {
require_module_lazy('friends');
- // TODO: add privacy checks!
DT('ReciprocalFriends')->add($this->id);
return null;
}
public function getFriendIDs() {
- return DT('ReciprocalFriends')->get($this->id);
+ if ($this->canSeeFriends()) {
+ return DT('ReciprocalFriends')->get($this->id);
+ }
+ return array();
}
/**
@@ -397,6 +399,7 @@ class EntPersonalUser extends EntProfile
$this->viewerCanSee,
array(
PrivacyConcepts::EXISTENCE,
+ PrivacyConcepts::FRIENDS,
// Note that we're fetching GENDER here because it's PAI
// so it's cheap and because we don't want to add a prepareGender
// call here if we don't have to.
@@ -418,6 +421,10 @@ class EntPersonalUser extends EntProfile
return must_prepare($this->viewerCanSee)->canSee();
}
+ protected function canSeeFriends() {
+ return must_prepare($this->viewerCanSee)->canSeeFriends();
+ }
+
# update your local master branch
git checkout master
git pull --rebase
# never do any work on master branch
# create & switch to new branch instead
git checkout -b my_branch
# rebase 'my_branch' onto master
git checkout my_branch
git rebase master
# list branches
git branch
# delete 'my_branch' branch
$ git branch -d my_branch
# shows status
$ git status
stage file, also remove conflict
$ git add <file>
revert file to head revision
$ git checkout -- <file>
commit change
$ git commit -a --amend
-a stages all modified files
--amend overwrites last commit
show all local history (amend commits, branch changes, etc.)
$ git reflog
show history (there is lot of options)
$ git log
$ git log --pretty=oneline --abbrev-commit --author=plamenko
$ git log -S"text to search"
show last commit (what is about to be send for diff)
$ git show
get the version of the file from the given commit
$ git checkout <commit> path/to/file
fetch & merge
$ git pull --rebase
resolving conflicts:
use ours:
$ git checkout --ours index.html
use theirs:
$ git checkout --theirs index.html
commit author:
$ git config --global user.name "Ognjen Dragoljevic"
$ git config --global user.email plamenko@fb.com
After doing this, you may fix the identity used for this commit with:
$ git commit --amend --reset-author
commit template:
/mnt/vol/engshare/admin/scripts/templates/git-commit-template.txt
rename a branch:
$ git branch -m old_branch new_branch
interactive rebase
$ git rebase -i master
pick
edit
make changes
...
$ git commit -a --amend
$ git rebase --continue
exec
$ arc diff
$ arc amend
$ git push --dry-run origin HEAD:master // remove dry-run to do actual push
...
to update commit message in phabricator
$ arc diff --verbatim#!/bin/bash
#
# Creates a new www sandbox managed by git.
#
# Usage: git-clone-www [dirname]
#
# dirname defaults to "www-git".
#
DIRNAME=${1:-www-git}
NFS_REPO=/home/engshare/git/tfb
# Are we running on a machine that has a local shared copy of the git repo?
if [ -d /data/git/tfb ]; then
# Yes. Reuse its objects directory.
echo "Cloning the local host's shared www repository..."
PARENT=/data/git/tfb
SHARE=-s
else
# Nope, copy the NFS server's objects locally so as not to be dog slow.
echo "Copying from the shared www repository on the NFS server..."
PARENT=$NFS_REPO
SHARE=
fi
if [ ! -d $HOME/local ]; then
echo "You don't seem to have a 'local' symlink in your home directory."
echo "Fix that and try again."
exit 1
fi
cd $HOME/local
if [ -d "$DIRNAME" ]; then
echo "You already have a $DIRNAME directory; won't overwrite it."
echo "Aborting."
exit 1
fi
# We clone the shared repository here rather than running "git svn clone"
# because it's much, much more efficient. And the clone has some options:
#
# -n = Don't check out working copy yet.
# -s = Reference the origin's .git/objects directory rather than copying.
# Saves gobs of disk space and makes the clone nearly instantaneous.
# We don't do this if there's no local-disk shared repo.
git clone $SHARE -n "$PARENT" "$DIRNAME"
cd "$DIRNAME"
# If we're sharing a local repository's objects, use the NFS server as a
# fallback so stuff doesn't break if we use this repo from another host
# that doesn't have a /data/git/tfb directory.
ALTERNATES=.git/objects/info/alternates
if [ -s $ALTERNATES ]; then
echo $NFS_REPO/.git/objects >> $ALTERNATES
fi
# We want to use the same remote branch name ("remotes/trunk") for git-svn
# and for fetches from the shared git repo, so set that up explicitly.
git config remote.origin.url "file://$PARENT/.git"
git config remote.origin.fetch refs/remotes/trunk:refs/remotes/trunk
git config --remove-section branch.master
# Enable the standard commit template
git config commit.template /home/engshare/admin/scripts/templates/git-commit-template.txt
# Enable recording of rebase conflict resolutions
git config rerere.enabled true
# Now fetch from the shared repo. This mostly just creates the new "trunk"
# branch since we already have the objects thanks to the initial "git clone".
git fetch origin
# Blow away the "origin/" branches created by "git clone" -- we don't need them.
rm -rf .git/refs/remotes/origin
# Now it's time to turn this plain old git repo into a git-svn repo. Really
# all we need is the svn-remote configuration (installed above) and a
# metadata file with some version information. git-svn is smart enough to
# rebuild the other stuff it needs.
echo ""
echo "Synchronizing with svn..."
git svn init -itrunk svn+ssh://tubbs/svnroot/tfb/trunk/www
# Now tweak the git-svn config a little bit so it's easier for someone to
# go add more "fetch" lines if they want to track svn-side branches in
# addition to trunk. This doesn't affect any of the existing history.
git config svn-remote.svn.url svn+ssh://tubbs/svnroot
git config svn-remote.svn.fetch tfb/trunk/www:refs/remotes/trunk
# Let git-svn update its mappings and fetch the latest revisions. This can
# spew lots of uninteresting output so suppress it.
git svn fetch > /dev/null
echo ""
echo "Checking out working copy..."
# We use git reset here because the git svn fetch might have advanced trunk
# to a newer revision than the master branch created by git clone.
git reset --hard trunk
if [ ! -d "$HOME/$DIRNAME" ]; then
echo ""
echo "Making home dir symlink: $HOME/$DIRNAME"
ln -s "local/$DIRNAME" "$HOME/$DIRNAME"
else
echo ""
echo "$HOME/$DIRNAME already exists; leaving it alone."
fi
echo ""
echo "All done. To make this your new main sandbox directory, run"
echo ""
echo " rm -rf ~/www"
echo " ln -s ~/$DIRNAME ~/www"
echo ""Lastly, I wanted to share something which I found quite amusing. Facebook’s MySQL password. This came from what seems to be a `print_r()` of an array which made its way in to production a few years ago.
array ( 'ip' => '10.21.209.92', 'db_name' => 'insights', 'user' => 'mark', 'pass' => 'e5p0nd4', 'mode' => 'r', 'port' => 3306, 'cleanup' => false, 'num_retries' => 3, 'log_after_num_retries' => 4, 'reason' => 'insights', 'cdb' => true, 'flags' => 0, 'is_shadow' => false, 'backoff_retry' => false, )Host: 10.21.209.92 (Private IP)
Database Name: insights
User: mark
Password: e5p0nd4Okay, so it’s not the most secure password. But Facebook’s database servers are heavily firewalled. Though if you do manage to break in to Facebook’s servers, there’s the password.
Edit: Mark Zuckerberg was an officer at the Jewish fraternity Alpha Epsilon Pi. The motto on their coat of arms is “ESPONDA”. 🙂
So what have we learnt today? I think the main thing to take away from this is you shouldn’t use public services such as Pastebin to post internal source code. Some creepy guy like me is going to collect it all and write about it. Another thing is to make sure debug information is never pushed to production. I didn’t put much effort in to this but there will be more of Facebook’s source code floating around out there.
Again I’d like to stress that everything I have posted here was already available on the Internet. All I needed to do was search for it. And here’s the download:
URL: facebook_source_code.zip
Password: sintheticlabs.com
If you enjoyed this post and want to see more, follow @SintheticLabs on Twitter.
Public HackerOne bug reports.
Public HackerOne bug reports.
Last Updated: 12th September, 2017
| Team | Bounty | Title |
|---|---|---|
| Legal Robot | – | design issue exists on login page |
| Legal Robot | – | Coding error ! |
| TTS Bug Bounty | – | {REDACTED}.data.gov subdomain takeover. |
| Legal Robot | – | Insufficient Security Configurability-Weak Registration Implementation-Allows Disposable Email Addresses |
| Legal Robot | – | I cant login to my account |
| TTS Bug Bounty | – | Email Spoofing – SPF record set to Neutral |
| TTS Bug Bounty | – | Email Spoofing – SPF record set to Neutral |
| Legal Robot | – | Improper error message |
| Legal Robot | – | Email Length Verification |
| TTS Bug Bounty | – | federalist.18f.gov vulnerable to Sweet32 attack |
| TTS Bug Bounty | – | Subdomain take-over of {REDACTED}.18f.gov |
| Legal Robot | – | Name can’t be numbers or email |
| Gratipay | – | Reflected XSS – gratipay.com |
| HackerOne ★ | – | IDOR on HackerOne Feedback Review |
| Gratipay | – | Gratipay rails secret token (secret_key_base) publicly exposed in GitHub |
| Legal Robot | – | Password Restriction On Change |
| Legal Robot | – | UX: JS error on Password Safety link |
| Gratipay | – | xss |
| Unikrn | $200 | HTML injection in email in unikrn.com |
| Legal Robot | – | Information disclosure |
| Rockstar Games | $500 | dom based xss in http://www.rockstargames.com/GTAOnline/ (Fix bypass) |
| Legal Robot | – | Special characters are not filtered out on profile fields |
| Legal Robot | – | Change password session fixed |
| Legal Robot | – | Weak Cryptography for Passwords |
| Legal Robot | $20 | No length limit in invite_code can cause server degradation |
| Legal Robot | $20 | CSP script-src includes “unsafe-inline” |
| Legal Robot | $20 | Improper validation of parameters while creating issues |
| Legal Robot | $100 | Update any profile |
| Legal Robot | – | Invalid Email Verification |
| Legal Robot | $20 | first name and last name restrictions bypass |
| Legal Robot | $20 | TabNabbing issue (due to taget=_blank) |
| Legal Robot | – | Tampering the mail id on chatbox |
| Legal Robot | $20 | Incorrect error message |
| Legal Robot | $20 | Incorrect email content when disabling 2FA |
| Legal Robot | $20 | Lengthy manual entry of 2FA secret |
| Trello | $128 | A CRLF injection into the redirect URL of https://trello.com/1/authorize can be used to cause a denial of service when later redirected to |
| Udemy | – | No password length restriction |
| ownCloud | – | owncloud.com open redirect |
| Quora | $500 | [Quora Android] Possible to steal arbitrary files from mobile device |
| WordPress | – | Clickjacking – https://mercantile.wordpress.org/ |
| Snapchat | $5,000 | RCE/LFI on test Jenkins instance due to improper authentication flow |
| Gratipay | – | Sub domain take over in gratipay.com |
| Ruby | – | Open aws s3 bucket s3://rubyci |
| Udemy | – | CSRF Token |
| Legal Robot | $40 | Code injection |
| Khan Academy | – | Weak Bithdate Validation Implemented on Sign Up |
| WakaTime | – | Impersonation of Wakatime user using Invitation functionality. |
| ownCloud | – | This is not the security issue. |
| Legal Robot | $20 | User enumeration from failed login error message |
| Udemy | – | Violation of secure design principle |
| Udemy | – | Weak Password |
| Legal Robot | – | Mixed Content over HTTPS |
| Brave Software | $200 | URL Spoof / Brave Shield Bypass |
| Khan Academy | – | Password Functionality not working correctly |
| Legal Robot | $20 | Change password logic inversion |
| Legal Robot | $20 | Profile fields validation bypass |
| arxius | – | No Email Verification and No email sent on Forget Pasword |
| Phabricator | – | Credential gets exposed |
| Legal Robot | – | LUCKY13 (CVE-2013-0169) effects legalrobot.com |
| WakaTime | – | Failure to check password history |
| Legal Robot | – | Create Api Key is not working |
| Legal Robot | $20 | Profile shows incorrect account creation date |
| Legal Robot | – | Password Reset page Session Fixation |
| Legal Robot | – | Lack of input validation in e-mail & user name, job title, company name field |
| Legal Robot | – | SSL : breach compression attack (CVE-2013-3587) effects legalrobot.com |
| Coinbase | – | Device confirmation Flaw |
| Rockstar Games | $500 | dom based xss in https://www.rockstargames.com/GTAOnline/ |
| Bitvise | $100 | The POODLE attack (SSLv3 supported) |
| Unikrn | $50 | Escaping images directory in S3 bucket when saving new avatar, using Path Traversal in filename |
| Boozt Fashion AB | $60 | Password reset token issue |
| Legal Robot | $20 | [Cross-domain Referer leakage] Password reset token leakage via referer |
| Automattic | $225 | XSS Vulnerability in WooCommerce Product Vendors plugin |
| Rockstar Games | $600 | CSRF Vulnerability allows attackers to steal SocialClub private token. |
| Dropbox | – | Missing URL sanitization in comments can be leveraged for phishing |
| Phabricator | – | Hyper Link Injection In email and Space Characters Allowed at Password Field. |
| Tor | – | [Android org.torproject.android] Possible to force list of bridges |
| Legal Robot | $20 | Token leakage by referrer header & analytics |
| Zomato | $500 | Restaurant payment information leakage |
| Unikrn | $40 | Flash CSRF: Update Ad Frequency %: [cp-ng.pinion.gg] |